Nmap is an open source network mapper that allows one to scan network of hosts, services, perform security assessment and auditing. This useful command comes with loads of options and capabilities, but you need to have expertise in using it. In this tutorial, I’ll try to introduce few command examples that can help you to identify possible vulnerable points in the hosts, entire subnet, operating system and services version detection, listing of services, interfaces, routes, mac identification etc…
So, here we go.
Some of the Linux flavor may not come with nmap installed, so you can install it using yum or apt-get depending on the operating system you are using.
# yum install nmap
or
# apt-get install nmap
Let’s start with scanning a single host:
Scanning single IP address (no root)
$ nmap 14.0.0.6
Sample output:
Host is up (0.00035s latency). Not shown: 999 closed ports PORT STATE SERVICE 22/tcp open ssh Nmap done: 1 IP address (1 host up) scanned in 1.50 seconds
Scanning multiple IP addresses (no root)
$ nmap 14.0.0.6 14.0.0.5
Scanning multiple IP addresses using comma as delimiter
$ nmap 14.0.0.6,5
The above command will scan 14.0.0.5 and 14.0.0.6 IP addresses
Scanning range of IP addresses (no root)
$ nmap 14.0.0.1-5
The above command will scan IP address starting from 14.0.0.1 to 14.0.0.5
Scanning IP address using wild-card (no root)
$ nmap 14.0.0.*
Scanning all IP addresses in a subnet
$ nmap 14.0.0.0/24
Scanning a host using domain name
$ nmap www.example.com
Scanning hosts reading from a text file
$ cat host-list.txt 14.0.0.1 www.example.com 14.0.0.2
$ nmap -iL host-list.txt
Scanning a subnet excluding a particular IP address
$ nmap 14.0.0.0/24 --exclude 14.0.0.1
Scan a subnet excluding list of IP addresses
$ nmap 14.0.0.0/24 --exclude 14.0.0.1,2
Scan a subnet excluding the list of IP addresses from a file
$ cat exclude-ips.txt 14.0.0.1,2,3,4,5
$ nmap 14.0.0.0/24 --excludefile exclude-ips.txt
Identify hostnames of all IPs in a subnet (no root)
$ nmap -sL 14.0.0.0/24
Perform PING sweep
Ping sweep is generally used to find out which hosts are alive in the network. Ping sweep can be used if you want to scan large number of hosts in a network.
# nmap -sP 14.0.0.6
Scan a single port of a particular IP address or host (no root)
$ nmap -p 22 14.0.0.6
Sample output:
Host is up (0.00066s latency). PORT STATE SERVICE 22/tcp open ssh Nmap done: 1 IP address (1 host up) scanned in 0.47 seconds
Scan a range of ports (no root)
$ nmap -p 15-23 14.0.0.6
Sample output:
PORT STATE SERVICE 15/tcp closed netstat 16/tcp closed unknown 17/tcp closed qotd 18/tcp closed unknown 19/tcp closed chargen 20/tcp closed ftp-data 21/tcp closed ftp 22/tcp open ssh 23/tcp closed telnet
Perform a fast scan of ports (100 most common ports) (no root)
$ nmap -F 14.0.0.6
Scan top $number of ports (no root)
$ nmap --top-ports 10 14.0.0.6
$ nmap --top-ports 2 14.0.0.6
Scan all ports (no root)
$ nmap -p- 14.0.0.6
The above command will scan all 65535 ports of a given IP address.
Detecting OS and Service information of a remote host (no root)
$ nmap -A 14.0.0.6
Sample output:
Starting Nmap 7.01 ( https://nmap.org ) at 2016-07-11 06:34 UTC Host is up (0.00029s latency). Not shown: 999 closed ports PORT STATE SERVICE VERSION 22/tcp open ssh OpenSSH 7.2p2 Ubuntu 4ubuntu1 (Ubuntu Linux; protocol 2.0) :::::::::::::::::::
Service detection (no root)
$ nmap -sV 14.0.0.6
Aggressive service detection (no root)
Nmap command relies on different methods to detect operating system and service information. The aggressive service detection is helpful when the service runs on an uncommon port (for e.g, SSH is expected to listen on port 22, but the remote host might be running the service on different port). The aggressive service detection is slower than the normal service detection, as the later one gets the information from the service banners.
$ nmap -sV --version-intensity 5 14.0.0.6
Sample output:
Host is up (0.00044s latency). Not shown: 999 closed ports PORT STATE SERVICE VERSION 22/tcp open ssh OpenSSH 7.2p2 Ubuntu 4ubuntu1 (Ubuntu Linux; protocol 2.0) Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel Service detection performed. Please report any incorrect results at https://nmap.org/submit/
Detecting Operating System (root)
The above service detection example will reveal the operating system information. It’s also possible to guess the operating system and its version using the below command as well.
Note: The OS detection requires root privilege.
$ nmap -O 14.0.0.6 TCP/IP fingerprinting (for OS scan) requires root privileges. QUITTING!
# nmap -O 14.0.0.6
# nmap -O --osscan-guess 14.0.0.6 Starting Nmap 7.01 ( https://nmap.org ) at 2016-07-11 08:39 UTC Host is up (0.00035s latency). Not shown: 999 closed ports PORT STATE SERVICE 22/tcp open ssh Aggressive OS guesses: Linux 3.1 (93%), Linux 3.2 (93%), AXIS 210A or 211 Network Camera (Linux 2.6.17) (92%), Android 5.0.2 (92%), Android 5.1 (92%), Linux 3.0 (92%), Linux 3.11 (92%), Linux 3.12 (92%), Linux 3.12 - 3.19 (92%), Linux 3.13 (92%)
# nmap -v -O --osscan-guess 14.0.0.6
Detect if a host is protected by a firewall (root)
When firewall is disabled in the remote host, the nmap scans all ports and says they are unfiltered as shown below:
# nmap -sA 14.0.0.6 Host is up (0.00042s latency). All 1000 scanned ports on henry2.cloudsecurity.in (14.0.0.6) are unfiltered
When the firewall is enabled in the remote host, the nmap says ports are filtered:
# nmap -sA 14.0.0.6 Nmap scan report for henry2.cloudsecurity.in (14.0.0.6) Host is up (0.00045s latency). All 1000 scanned ports on henry2.cloudsecurity.in (14.0.0.6) are filtered
Scanning using NSE scripts
There are about 400+ NSE (Nmap Scripting Engine) scripts that can be used with nmap and each script comes with a good documentation. In order to identify the list of scripts installed in your machine, run the below command:
# locate nse |grep script ::::::::::::::::::::: /usr/share/nmap/scripts/ssl-enum-ciphers.nse /usr/share/nmap/scripts/ssl-google-cert-catalog.nse /usr/share/nmap/scripts/ssl-heartbleed.nse /usr/share/nmap/scripts/ssl-known-key.nse /usr/share/nmap/scripts/ssl-poodle.nse /usr/share/nmap/scripts/sslv2.nse /usr/share/nmap/scripts/sstp-discover.nse /usr/share/nmap/scripts/stun-info.nse /usr/share/nmap/scripts/stun-version.nse /usr/share/nmap/scripts/stuxnet-detect.nse /usr/share/nmap/scripts/supermicro-ipmi-conf.nse /usr/share/nmap/scripts/svn-brute.nse /usr/share/nmap/scripts/targets-asn.nse /usr/share/nmap/scripts/targets-ipv6-map4to6.nse /usr/share/nmap/scripts/targets-ipv6-multicast-echo.nse /usr/share/nmap/scripts/targets-ipv6-multicast-invalid-dst.nse /usr/share/nmap/scripts/targets-ipv6-multicast-mld.nse /usr/share/nmap/scripts/targets-ipv6-multicast-slaac.nse /usr/share/nmap/scripts/targets-ipv6-wordlist.nse /usr/share/nmap/scripts/targets-sniffer.nse /usr/share/nmap/scripts/targets-traceroute.nse /usr/share/nmap/scripts/targets-xml.nse :::::::::::::
DNS Brute force to identify sub domains of a given domain (no root)
nmap allows one to identify the list of sub-domains for a given host. Identifying sub-domains of a hosts can reveal new targets while performing security assessment. To do that, dns-brute.nse script has to be used.
$ nmap -p 80 --script dns-brute.nse example.com
Sample output:
PORT STATE SERVICE 80/tcp open http Host script results: | dns-brute: | DNS Brute-force hostnames: | www.example.com - 93.184.216.34 |_ www.example.com - 2606:2800:220:1:248:1893:25c8:1946
Identifying virtual hosts on a given host (no root)
The given domain name may host multiple websites using virtual hosts feature of the web servers. You can identify virtual hosts using hostmap-bfk.nse script.
$ nmap -p 80 --script hostmap-bfk.nse nmap.org Host script results: | hostmap-bfk: | hosts: | mail.nmap.org | 45.33.49.119 | 119.49.33.45.in-addr.arpa | ack.nmap.org | sectools.org | svn.nmap.org | insecure.com | mail.seclists.org | seclists.org | mirror.sectools.org | www.insecure.org | nmap.org | insecure.org | www.nmap.org |_ www.insecure.com
Identify the geographical location of given host
# nmap --traceroute --script traceroute-geolocation.nse -p 80 example.com
Sample output:
:::::::::::::::: Host script results: | traceroute-geolocation: | HOP RTT ADDRESS GEOLOCATION | 1 0.44 14.0.0.1 23,113 China (Guangdong) | 2 0.88 10.180.141.1 - ,- | 3 1.58 144.16.192.34 20,77 India () | 4 1.87 14.139.1.30 20,77 India () | 5 1.61 10.118.248.45 - ,- | 6 11.62 10.161.18.5 - ,- | 7 ... | 8 13.32 10.255.221.34 - ,- | 9 14.71 115.249.209.6 18,72 India (Mah\xC4\x81r\xC4\x81shtra) | 10 ... | 11 ... | 12 ... | 13 293.92 xe-3-0-6.0.cjr01.sin001.flagtel.com (62.216.129.201) 51,0 United Kingdom () | 14 293.77 ge-2-0-0.0.pjr01.hkg005.flagtel.com.25.95.85.in-addr.arpa (85.9 5.25.41) 51,0 United Kingdom () | 15 168.70 so-1-0-0.0.pjr01.wad001.flagtel.com (85.95.25.193) 51,0 United Kingdom () | 16 168.13 so-2-2-0.0.pjr01.wad001.flagtel.com (85.95.25.37) 51,0 United Kingdom () | 17 293.97 so-2-1-0.0.pjr01.lax002.flagtel.com (85.95.25.17) 51,0 United Kingdom () | 18 275.17 any2ix.coresite.com (206.223.143.232) 38,-97 United States () |_ 19 295.32 93.184.216.34 42,-70 United States (Massachusetts) :::::::::::::::::::::::::::::::::
For example, identify list of HTTP related scripts:
# locate nse |grep http /usr/share/nmap/nselib/http.lua /usr/share/nmap/nselib/httpspider.lua /usr/share/nmap/nselib/data/http-default-accounts-fingerprints.lua /usr/share/nmap/nselib/data/http-devframework-fingerprints.lua /usr/share/nmap/nselib/data/http-fingerprints.lua /usr/share/nmap/nselib/data/http-folders.txt /usr/share/nmap/nselib/data/http-sql-errors.lst /usr/share/nmap/nselib/data/http-web-files-extensions.lst /usr/share/nmap/scripts/http-adobe-coldfusion-apsa1301.nse /usr/share/nmap/scripts/http-affiliate-id.nse /usr/share/nmap/scripts/http-apache-negotiation.nse /usr/share/nmap/scripts/http-auth-finder.nse /usr/share/nmap/scripts/http-auth.nse /usr/share/nmap/scripts/http-avaya-ipoffice-users.nse /usr/share/nmap/scripts/http-awstatstotals-exec.nse /usr/share/nmap/scripts/http-axis2-dir-traversal.nse /usr/share/nmap/scripts/http-backup-finder.nse /usr/share/nmap/scripts/http-barracuda-dir-traversal.nse /usr/share/nmap/scripts/http-brute.nse /usr/share/nmap/scripts/http-cakephp-version.nse /usr/share/nmap/scripts/http-chrono.nse /usr/share/nmap/scripts/http-cisco-anyconnect.nse /usr/share/nmap/scripts/http-coldfusion-subzero.nse /usr/share/nmap/scripts/http-comments-displayer.nse /usr/share/nmap/scripts/http-config-backup.nse /usr/share/nmap/scripts/http-cors.nse /usr/share/nmap/scripts/http-cross-domain-policy.nse /usr/share/nmap/scripts/http-csrf.nse /usr/share/nmap/scripts/http-date.nse /usr/share/nmap/scripts/http-default-accounts.nse /usr/share/nmap/scripts/http-devframework.nse /usr/share/nmap/scripts/http-dlink-backdoor.nse /usr/share/nmap/scripts/http-dombased-xss.nse /usr/share/nmap/scripts/http-domino-enum-passwords.nse /usr/share/nmap/scripts/http-drupal-enum-users.nse /usr/share/nmap/scripts/http-drupal-enum.nse /usr/share/nmap/scripts/http-enum.nse /usr/share/nmap/scripts/http-errors.nse /usr/share/nmap/scripts/http-exif-spider.nse /usr/share/nmap/scripts/http-favicon.nse /usr/share/nmap/scripts/http-feed.nse /usr/share/nmap/scripts/http-fetch.nse /usr/share/nmap/scripts/http-fileupload-exploiter.nse /usr/share/nmap/scripts/http-form-brute.nse /usr/share/nmap/scripts/http-form-fuzzer.nse /usr/share/nmap/scripts/http-frontpage-login.nse /usr/share/nmap/scripts/http-generator.nse /usr/share/nmap/scripts/http-git.nse /usr/share/nmap/scripts/http-gitweb-projects-enum.nse :::::::::::::::::::::
From the above output, you can copy the script name and use it with –script option.
Get HTTP service information (no root)
There are many scripts to get HTTP service information such as title of the web page, HTTP headers, finding various known paths of web application etc…
$ nmap --script=http-title 14.0.0.5 Host is up (0.0000070s latency). Not shown: 998 closed ports PORT STATE SERVICE 22/tcp open ssh 80/tcp open http |_http-title: Apache2 Ubuntu Default Page: It works
Get HTTP header information (no root)
$ nmap --script=http-headers 14.0.0.5 PORT STATE SERVICE 22/tcp open ssh 80/tcp open http | http-headers: | Date: Mon, 11 Jul 2016 07:08:05 GMT | Server: Apache/2.4.18 (Ubuntu) | Last-Modified: Mon, 11 Jul 2016 07:04:49 GMT | ETag: "2c39-53756c49f4280" | Accept-Ranges: bytes | Content-Length: 11321 | Vary: Accept-Encoding | Connection: close | Content-Type: text/html | |_ (Request type: HEAD)
Identify known paths of HTTP web application (no root)
$ nmap --script=http-enum 14.0.0.5 80/tcp open http | http-enum: |_ /server-status/: Potentially interesting folder
Detect Heartbleed SSL vulnerability (no root)
You might have heard of SSL vulnerability heartbleed. Nmap command can be used to detect this vulnerability as shown below:
nmap -sV -p 443 --script=ssl-heartbleed 14.0.0.0/24
Identify whois of a domain name (no root)
$ nmap -sV --script=whois-domain.nse www.example.com
Sample output:
Host script results: | whois-domain: | | Domain name record found at whois.iana.org | % IANA WHOIS server | % for more information on IANA, visit http://www.iana.org | % This query returned 1 object | | domain: EXAMPLE.COM | | organisation: Internet Assigned Numbers Authority | | created: 1992-01-01 | source: IANA |_
TCP Syn and UDP Scan (root)
# nmap -sS -sU -PN 14.0.0.6
The above command will scan 2000 common TCP and UDP ports. The –PN option requests nmap to skip ping scan and assume that the host is up. The option is useful when the remote machine has firewall enabled and drops all ICMP packets.
TCP connect scan (no root)
$ nmap -sT 14.0.0.6
The above command requests the OS to establish TCP connection to the 1000 common ports instead of sending TCP SYN packet.
Scan an IPv6 addresses (no root)
All the above example commands were scanning an IPv4 address, but you can scan IPv6 address as well. To do that, you need to use option ‘-6‘ followed by an IPv6 address.
$ nmap -6 2001:db8:000:3eff:fe52:77
List host Interfaces and routes (no root)
$ nmap --iflist Starting Nmap 7.01 ( https://nmap.org ) at 2016-07-11 09:53 UTC ************************INTERFACES************************ DEV (SHORT) IP/MASK TYPE UP MTU MAC lo (lo) 127.0.0.1/8 loopback up 65536 lo (lo) ::1/128 loopback up 65536 ens3 (ens3) 14.0.0.5/24 ethernet up 1450 FA:16:3E:C0:14:5F ens3 (ens3) fe80::f816:3eff:fec0:145f/64 ethernet up 1450 FA:16:3E:C0:14:5F **************************ROUTES************************** DST/MASK DEV METRIC GATEWAY 169.254.169.254/32 ens3 0 14.0.0.1 14.0.0.0/24 ens3 0 0.0.0.0/0 ens3 0 14.0.0.1 ::1/128 lo 0 fe80::f816:3eff:fec0:145f/128 lo 0 fe80::/64 ens3 256 ff00::/8 ens3 256
Save Nmap outputs to a text file
$ nmap -oN nmap_text.txt 14.0.0.6
Save Nmap output as XML
$ nmap -oX nmap_xml.xml 14.0.0.6
Save output in a format for grep
$ nmap -oG nmap_grep.txt 14.0.0.6
Save Nmap output in all formats
$ nmap -oA allformats_file 14.0.0.6
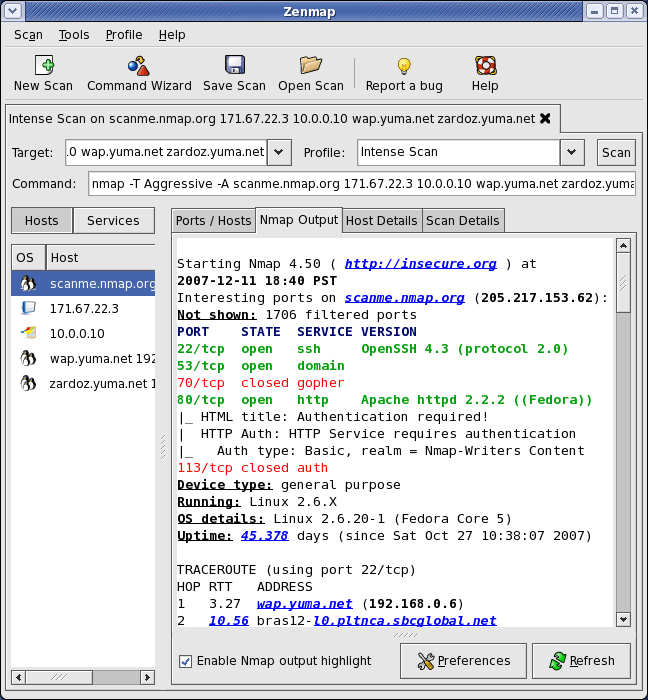
Nmap with GUI
Download Zenmap (or) install it using apt-get/yum
$ sudo apt-get install zenmap